- Home
-
Company
Join Our Team
Start working at the pioneering software development company in India and experience your career reaching the acme.
-
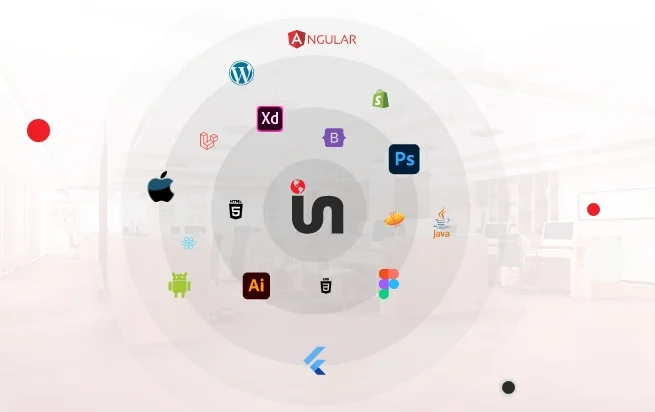
Services
Hire Dedicated Developers
Get a team of experienced and dedicated developers who can convert your business idea into reality and work as your extended development team.
-
Industries
Discuss Your Project
Any Idea For New Project we have Business Experts to ensure Success.
-
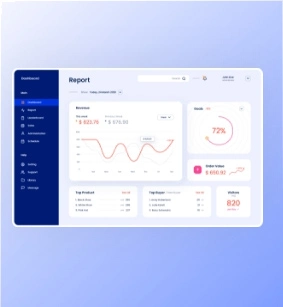
Digital Marketing
Join Our Team
Start working at the pioneering software development company in India and experience your career reaching the acme.
-
Hire Developers
Join Our Team
Start working at the pioneering software development company in India and experience your career reaching the acme.
- Blog